Join us in this episode as we uncover the importance of hashing in maintaining the security of digital content as it moves across networks. Through a demonstration, we show how hashing acts as a safeguard to ensure that data remains unchanged as it travels through different channels.
We also delve into the world of digital signatures, explaining how they verify the authenticity and integrity of electronic documents and messages. Additionally, we take a look at MACSec and its role in securing communication over Ethernet networks.
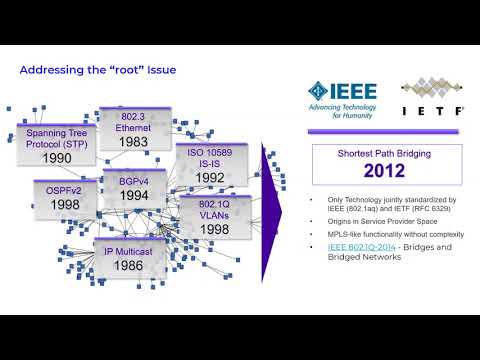
In the midst of complex network security management, we stress the importance of simplicity over complexity. We champion straightforward and efficient approaches to network security, debunking the myth that intricate solutions are the only way to protect digital assets.
Don’t miss this informative guide to hashing, digital signatures, MACSec, and practical strategies for managing network security.
Learn more about how Extreme applications and hardware platforms can enhance security for users, applications, and networks: https://www.extremenetworks.com/solutions/security
Follow Extreme Networks Training on LinkedIn for more content like this: https://www.linkedin.com/showcase/76160180
𝗖𝗵𝗮𝗽𝘁𝗲𝗿𝘀
00:00 Introduction
00:35 Digital Signatures
03:00 Hashing
07:20 MACsec
08:24 Complexity
12:07 QR code for supporting info
12:46 Episode Summary